Recently I had a request to integrate Azure AD for SSO into SailPoint IdentityNow. And as weird as it sounds previously integrations had been either with Active Directory or other IDentity-as-a-Service Providers (IDaaS).
It shouldn’t be too hard. I had visited the Service Provider IdentityNow Administration configuration screen before. And had setup identity federation many times before. Chances are though, you’re reading this because you are attempting to also integrate Azure AD for SSO into SailPoint IdentityNow. And the documentation you’ve found is incomplete and in a number of cases obsolete and contradictory.
In this post then I show how I configured Azure AD for SSO into SailPoint IdentityNow both as an IdP and Service initiated configuration.
Registering SailPoint IdentityNow into Azure AD from the Application Gallery
This is the easiest part. The documentation for this is pretty good, although outdated.
After running through that tutorial check your configuration against mine. You’ll notice I also have a Logout URL.
Identifier (Entity ID) https://<IDN Tenant>.identitynow.com/sp
Reply URL https:// <IDN Tenant>.login.sailpoint.com/saml/SSO/alias/ <IDN Tenant> -sp
Sign on URL https:// <IDN Tenant> .identitynow.com/
Logout URL https:// <IDN Tenant> .identitynow.com/logout

Next you will want to edit the Attributes and Claims. Select Edit from the Attributes and Claims section. Then select the three dots for the Unique User Identifier (Name ID)

Change the Name Identifier format to be Unspecified and select Save.

Finally download the SAML Signing Certificate in Base64 format and copy the properties from Section 4.

Configuring SailPoint IdentityNow to use Azure AD and an Identity Provider
From the SailPoint IdentityNow Admin Portal under Global Settings => Security Settings => Service Provider make the following configuration changes.
Entity ID https://sts.windows.net/<AAD Tenant>
Login URL (POST) https://login.microsoftonline.com/ <AAD Tenant>/saml2
Login URL (Redirect) https:// login.microsoftonline.com/<AAD Tenant> /saml2
Logout URL https:// <IDN Tenant> .login.sailpoint.com/signout
Identity Mapping Attribute uid
SAML NameID Unspecified
SAML Binding Post
Exclude Requested Authentication Context checked

The Certificate upload/import for me never worked through the UI. If it does for you, awesome. If not here is how I did it.
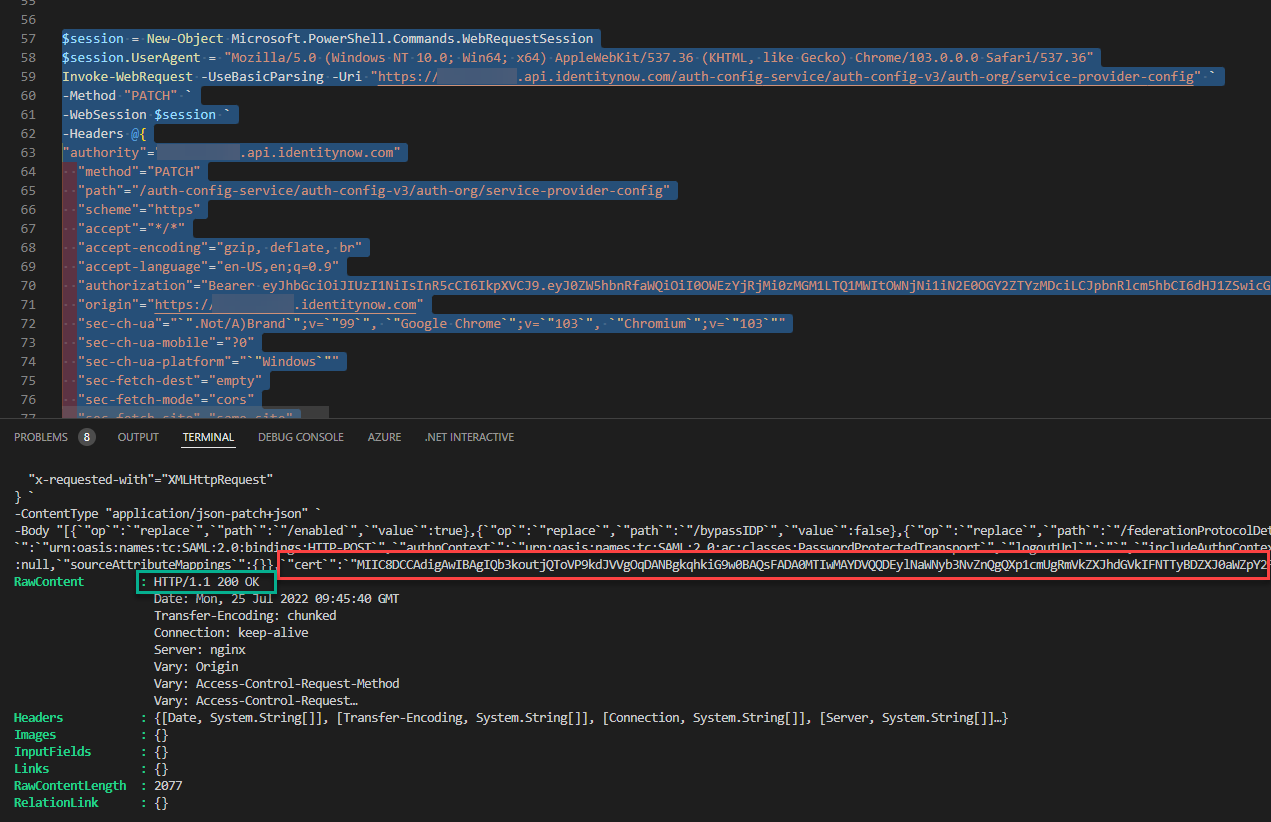
In my browser with the Service Provider screen open I selected F12 to open Developer Tools. Select Network then from the IdentityNow Admin page under Service Provider make a subtle change such as untick Exclude Requested Authentication Context and select Save. From the list of calls to the page find the one that is the PATCH to save the config. Right click on it and choose Copy as PowerShell.

Paste that into a PowerShell console such as VSCode.

Edit the last line (Body) where there is the cert section. Between the two `” insert your Base64 certificate text after removing the –BEGIN… and —END lines and all the line breaks so it is one long string.

Select the whole PowerShell command and run it (F8) which will update your configuration with your certificate.
Testing Azure AD for SSO into SailPoint IdentityNow
Before you can test the integration, you will need to assign the application to a user to test with. The user must already exist in IdentityNow synchronized to an Identity Profile from an appropriately configured Azure AD Source.

Logged in to Azure AD as a user assigned the SailPoint IdentityNow application above, navigating to My Applications https://myapps.microsoft.com will show the SailPoint IdentityNow Application. This can be selected and SSO achieved using the SAML2 configuration completed above. This is the IdP initiated Azure AD SSO to IdentityNow.
To test Service Provider initiated SSO to IdentityNow using Azure AD navigate to https://<tenant>.identitynow.com which will redirect to Azure AD for authentication and to get an SAML token and redirect back to IdentityNow performing SSO.

Summary
In this post I’ve shown the necessary configuration in both Azure AD and IdentityNow to achieve both IdP and SP initiated Single Sign-On.


