If you’ve ever needed to debug a Microsoft Entra (Azure AD) authentication flow, you’ll know how painful it can be. There are a number of browser extensions available, but in my view they fall short when you want to debug Microsoft centric nuances. That is why I built Entra Auth Tracer.
Entra Auth Tracer is a free, open-source Chromium-based browser extension that performs real-time, in-browser inspection of authentication and identity traffic. It is available now on GitHub and will be listed on the Chrome Web Store and Microsoft Edge Add-ons Store.
What is Entra Auth Tracer?
Entra Auth Tracer extends the foundation of the well-known SimpleSAMLphp SAML-tracer browser extension (licensed BSD-2-Clause) to support the full breadth of modern identity protocols and providers.
Where SAML-tracer focuses on SAML traffic, Entra Auth Tracer adds deep support for OAuth 2.1, OpenID Connect, FIDO2/Passkeys, Entra Verified ID / Decentralised Identity (DID), and Entra-specific JWT claim enrichment — across Microsoft Entra, Okta, AWS Cognito, Google, ADFS, Shibboleth, IdentityServer/Duende, SAP, and any standards-compliant SAML 2.0, OIDC, or OAuth 2.x provider.
Everything runs locally inside your browser. No data leaves your machine.
Key Features
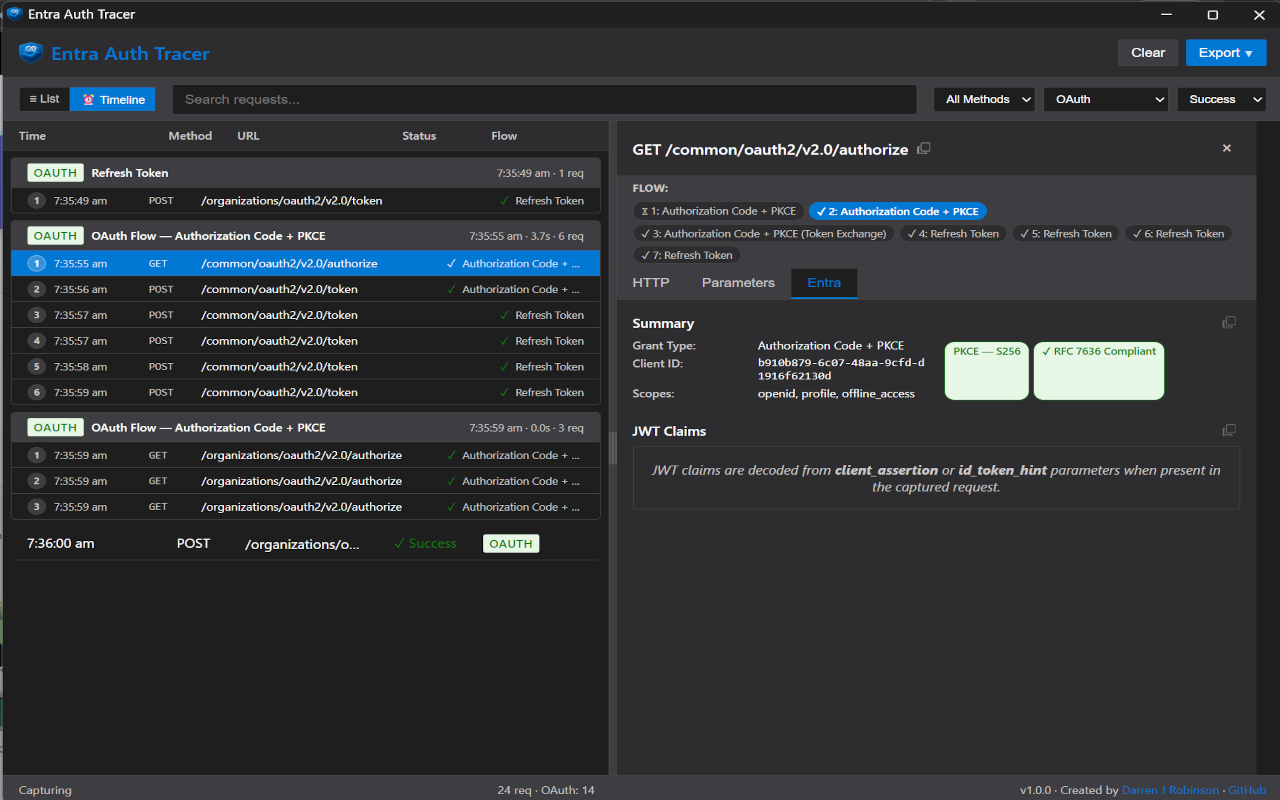
OAuth 2.1 / OIDC Flow Detection
The extension automatically detects OAuth 2.x and OIDC traffic across a broad set of endpoints and providers including Microsoft Entra, Okta, AWS Cognito, Google/Firebase, IdentityServer/Duende, and any generic OAuth 2.x endpoint. Flow and grant type intelligence covers Authorization Code + PKCE (with RFC 7636 compliance checking), Device Code flows with correlated timeline, Client Credentials, Refresh Token, ROPC/Implicit (flagged with deprecation warnings), and OIDC Discovery.
Client authentication decoding surfaces the method used by the OAuth client at the token endpoint — including credentials that only appear in HTTP headers. This means client_secret_basic (decoded from the Authorization header), client_secret_post, Digest auth, and private_key_jwt / client_assertion JWTs are all decoded and presented in the UI.
Entra JWT Claims Decoder
A key feature I’ve built a PowerShell module for previously is for anyone working with Microsoft Entra is the dedicated JWT claims decoder. The extension maps 40+ Entra-specific JWT claims to human-readable labels and tooltips, decodes all 18 Authentication Method Reference (AMR) values to plain English (Password, FIDO2/Passkey, Windows Hello for Business, SMS OTP, Windows Integrated Auth, Federated IdP, and more), decodes the platf claim to OS names, surfaces Continuous Access Evaluation (CAE) capability badges, and provides per-token security assessments — including expired token warnings, long-lived lifetime flags (> 60 min), guest account detection, and public client indicators.
SAML 2.0 and WS-Federation
All the SAML capabilities you’d expect are there:
- POST binding,
- Redirect binding,
- Artifact binding,
- SAML ECP,
- ADFS SAML via /adfs/ls/,
- Shibboleth SP ACS and logout endpoints,
- and full WS-Federation wresult payload decoding.
This builds directly on the SimpleSAMLphp SAML-tracer foundation and extends it significantly
FIDO2 / Passkey Analysis
Entra Auth Tracer captures and decodes all three HTTP phases of a WebAuthn/Passkey sign-in:
- the options/pre-flight challenge fetch,
- the signed assertion POST (with full CBOR decoding of clientDataJSON and authenticatorData,
- flag decomposition, and AAGUID-based authenticator identification for Windows Hello, YubiKey, and other FIDO2 hardware keys), and the resulting OAuth token exchange confirming amr=fido.
Note: the actual signing step inside the browser platform (navigator.credentials.get()) never travels over HTTP, so no extension can see it.
Entra Verified ID / Decentralised Identity (DID)
This is probably the most niche but most useful feature for anyone experimenting with Entra Verified ID and developing locally. When building issuance and presentation flows and testing locally the extension captures and decodes the full Verified ID lifecycle: issuance requests, presentation/verification requests, DID document resolution, credential status checks, and OID4VP/OID4VCI flows. It surfaces the credential type, authority, request ID, callback URL, and key warnings such as localhost callback URLs and PIN requirements. Both the Verified ID service calls and the resulting OAuth token exchange will appear in the timeline.
Timeline View and Enhanced UI
The UI takes a Microsoft Fluent-inspired design approach with full dark mode support and WCAG 2.1 AA accessibility. Key UI capabilities include:
- Timeline View — toggle between list and timeline modes, with correlated requests grouped into flow cards showing step sequence and duration.
- Flow Correlation — related requests (Device Code sessions, OAuth clientId windows) are automatically detected and soft-highlighted with a Flow chip strip in the detail header.
- Advanced Filtering — real-time search, method, flow-type, and status filters.
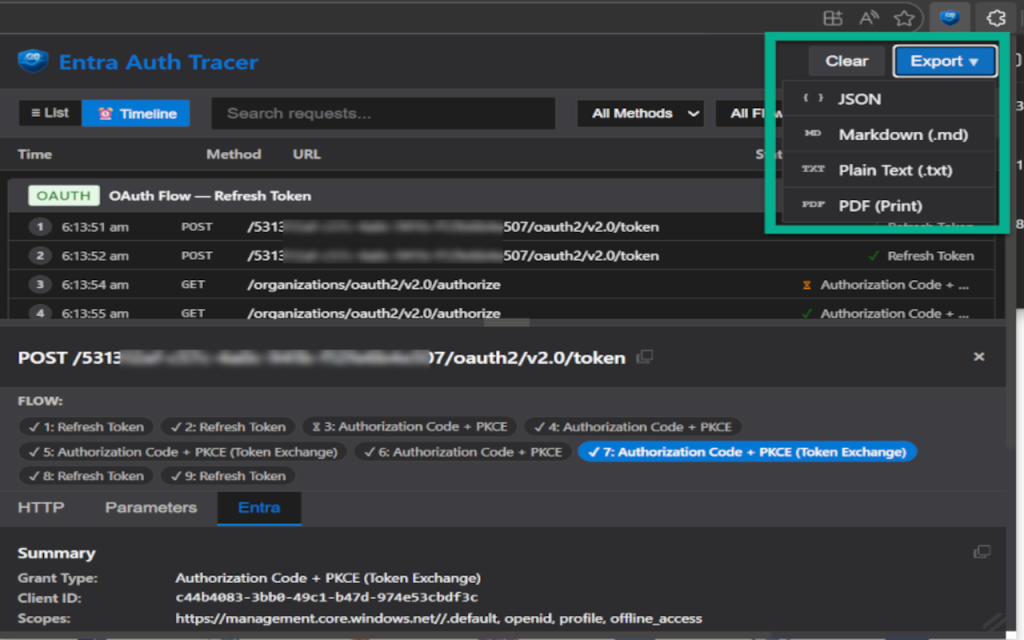
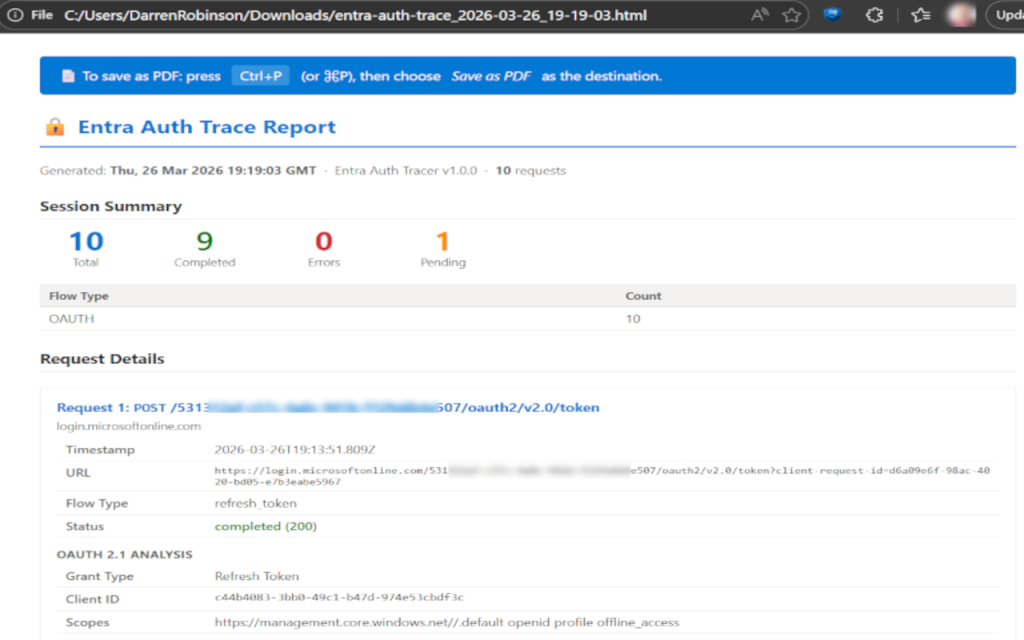
- Multi-format Export — export captured sessions as JSON, Markdown, plain text, or PDF (print-optimised HTML).
- Status Bar Breakdown — live per-category request counts (SAML, OAuth, FIDO2, Device Code) plus error count, updated in real time.
- Extension Icon Badge — a live event-counter badge on the toolbar icon increments on each captured auth event and resets when the popup is opened.
Privacy and Security
All analysis happens locally in your browser. The extension does not send data to any external servers. Client secrets and refresh tokens are automatically redacted in the UI. Captured request data is cleared when the extension is closed. Full details are in the Privacy Policy in the GitHub repository.
Installation
The extension is available to install in three ways:
- From the Chrome Web Store or Microsoft Edge Add-ons Store: search for “Entra Auth Tracer” (store listing coming soon).
- From a GitHub Release (recommended for testers): download the latest EntraAuthTracer-vX.X.X.zip from the Releases page, unzip it, navigate to chrome://extensions/ or edge://extensions/, enable Developer mode, click Load unpacked, and select the unzipped folder.
- From source: clone the repository, run npm install and npm run build, then load the dist folder as an unpacked extension.
Get Started
Entra Auth Tracer is open source, free to use, and contributions are welcome. Head to the GitHub repository to grab the latest release, raise issues, or contribute a feature branch.


